Permissions
As of AdminUI 2.2, you can now assign AdminUI permissions to users as a function of the claims they hold. This will then allow some administrators to have access to just user configuration and other access to IdentityServer related configuration.
Currently, there are three permissions available:
User Manager: The User Manager permission grants control over User, and Role management
IdentityServer Manager: The IdentityServer Manager permission allows users to create and modify ClaimTypes, Client Applications, Identity Resources, and Protected Resources
All: The final permission, All, allows for all of the above, and control over Access Policy Management itself.
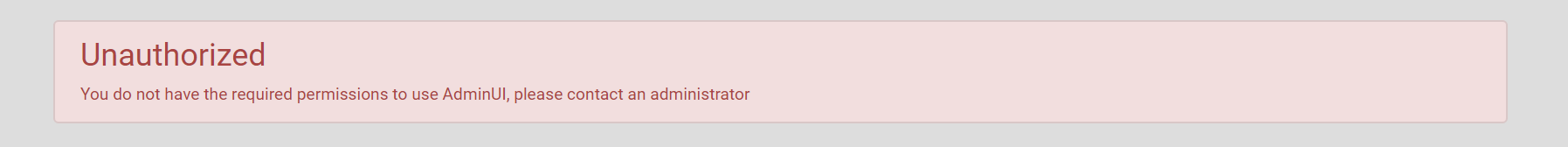
These permissions will affect both what actions users can perform against AdminUI’s API and the AdminUI UI. If a user does not have any AdminUI permissions they will be greeted with an unauthorized screen after logging in.
Don’t worry, we’ve left in the old ‘AdminUI Administrator’ role, mapping it to the ‘All’ permission so your current users won’t lose their access to AdminUI.
Example Setup
Users with the ‘All’ permission can manage the access policy however as in the example below I’ve created a role called ‘AdminUI User’ and mapped it to both the ‘User Manager’ and ‘IdentityServer Manager’ permissions.
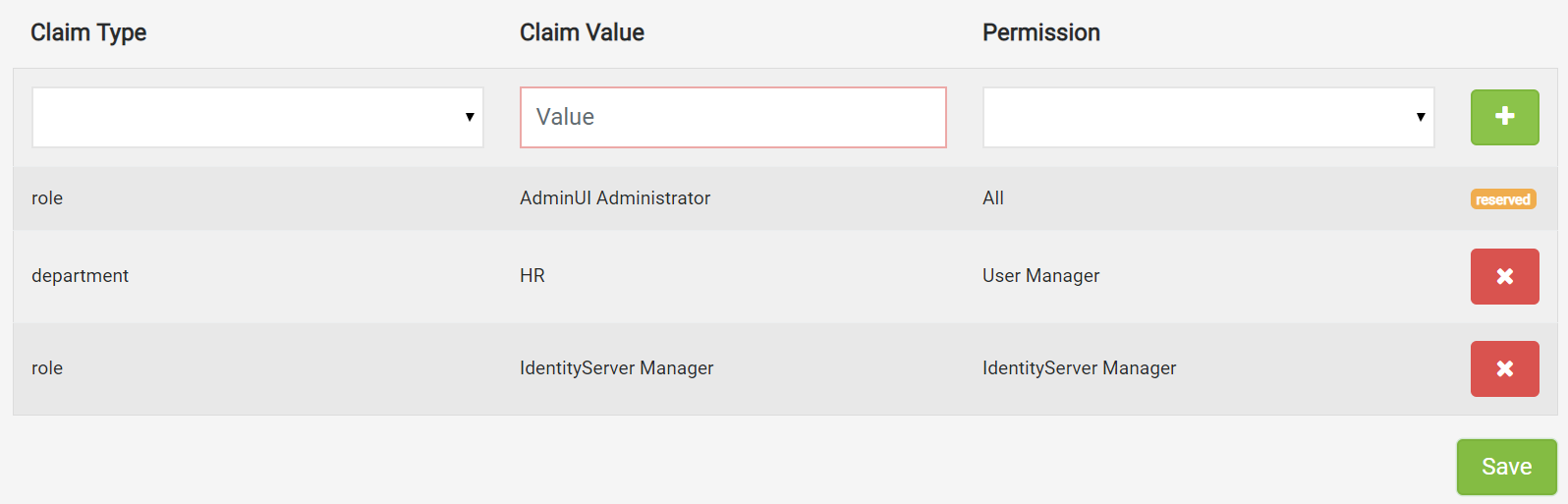
In effect, users with this role will have access to most of the screens and API in AdminUI but wouldn't be able to access or modify the access policy.
Users without the All permission will no longer be able to assign a role claim of value ‘AdminUI User’ in order to prevent unauthorized privilege escalation.
Be careful when creating new access policies as you may unintentionally elevate users. For example, if they already have the claims your are assigning permission to, they would automatically be given this new access. Equally, when removing access policies, users that rely on that policy for access will lose their permissions for AdminUI.
Installation
If you already have AdminUI installed then just update to AdminUI 2.2 to use this feature. Otherwise, if you would like to access a demo of AdminUI or if your license’s update period has expired and you would like to get access to the latest features, contact our sales team at sales@rocksolidknowledge.com.